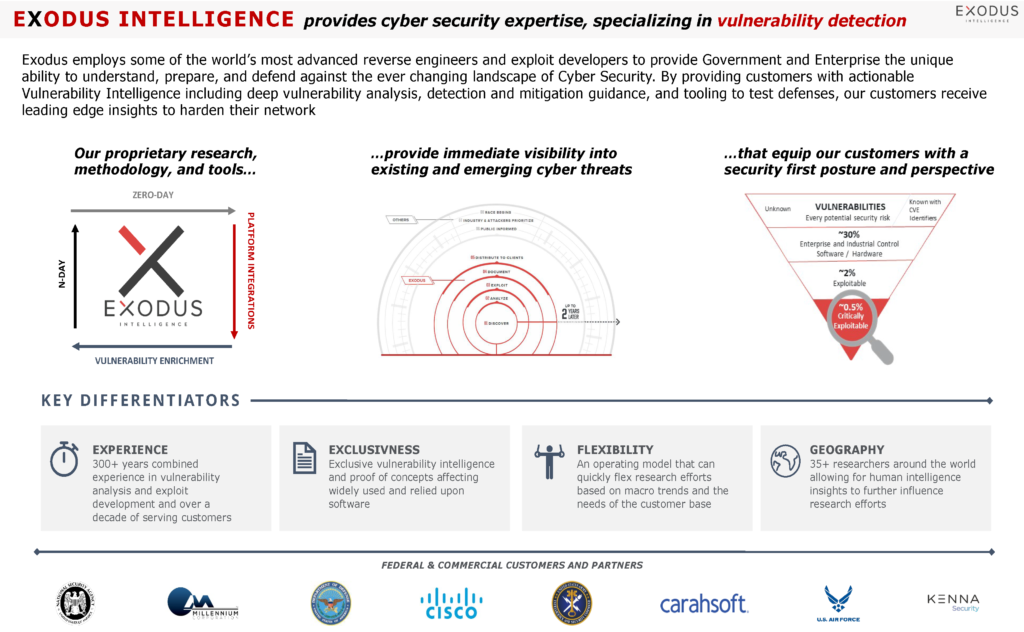
Exodus Intelligence Launches EVE Vulnerability Intelligence Platform Targeting Commercial Enterprises
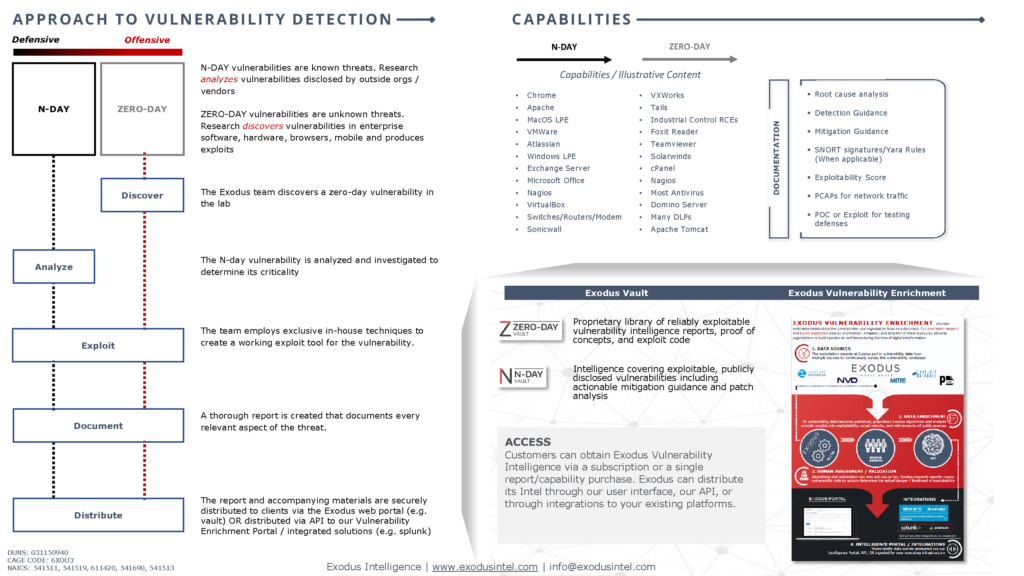
Today Exodus Intelligence is excited to announce EVE (Exodus Vulnerability Enrichment), our world-class vulnerability intelligence platform. EVE allows a wide range of security operations professionals to leverage Exodus’ state-level vulnerability research. This allows those professionals to prioritize mitigation and remediation efforts, enrich event data and incidents, be alerted to new noteworthy vulnerabilities relevant to their systems, and take advantage of many other available use cases valuable in defending their critical infrastructure.
EVE makes our robust intelligence available for the first time to enterprises for use in the defense of growing cyberattacks. The API to the Exodus body of research enables us to provide simple, out of the box integration with SIEMs, SOARs, ticketing systems and other infrastructure components that can employ contextual data. Additionally, it enables security operations teams to develop their own custom tooling and applications and integrate our vulnerability research.
Organizations with the ability to develop automation playbooks and other tools have been able to enrich available security data, enhance investigation and incident response capabilities, prioritize vulnerability remediation efforts, and more. We can now expand that capability and visibility to the rest of the security operations team with EVE.
EVE provides users with an intuitive interface to Exodus’ intelligence corpus made up of original research, machine learning analysis, and carefully curated public data. This interface includes regular automated updates to intelligence data, integration with environment-specific platform and vulnerability data, interactive visualizations that operationalize the research data for SOC analysts and risk management personnel, multidimensional search capability including filters which narrow results to only vulnerabilities that exist in the user’s environment and are likely to be exploited, and the ability to schedule searches to run on a recurring basis and email alerts to the user.
EVE capabilities include:
- Dynamic, automated intelligence feed: Vulnerability research data is updated at minimum once per day with likelihood of a vulnerability to be exploited (XI Score), mitigation guidance, and other original research combined with curated public vulnerability data to maximize visibility of the attack surface.
- Integration with the IT ecosystem: CPE data from vulnerability scans of the infrastructure can be input into EVE and applied as context to searches and visualizations keeping focus on relevant vulnerabilities.
- Smart data visualization: The dashboard provides a wealth of information including a real-time likelihood that an existing vulnerability will be exploited in the environment, vulnerabilities grouped and sorted by categories such as attack vector or disclosure month, and which platforms in the environment have the most vulnerabilities. All visualizations are interactive allowing the user to drill into the vulnerability details making the data actionable.
About Exodus Intelligence
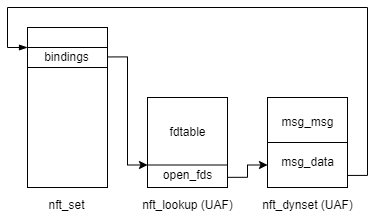
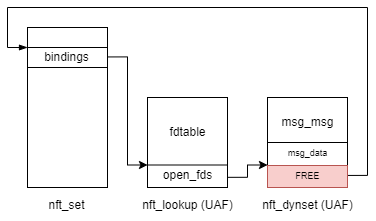
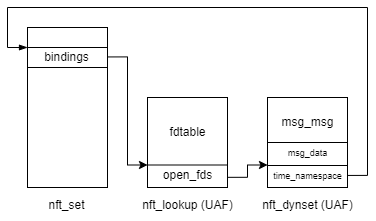
We provide clients with actionable information, capabilities, and context for proven exploitable vulnerabilities. Our world class team of vulnerability researchers discover hundreds of exclusive Zero-Day vulnerabilities, providing our clients with this knowledge before the adversaries find them. Our research also extends into the world on N-Day research, where we select critical N-Day vulnerabilities and complete research to prove whether these vulnerabilities are truly exploitable in the wild.
For more information, visit www.exodusintel.com or contact info@exodusintel.com for further discussion.