We are pleased to announce the offering of our next training course. This is a 5 day course and will focus on vulnerability research on embedded systems.
Instructors
David Barksdale – David is Director of Research at Exodus Intelligence and manages the 0day team. David is an expert in software and hardware reverse engineering. Last year he won a PWNIE award for Best Server-Side Bug for a Cisco firewall RCE exploit. David started hacking at a young age and was published in the Summer 2001 issue of 2600. In fall 2003 he reverse engineered Yahoo! Messenger’s new authentication protocol and wrote an exploit for a 0-day vulnerability in Microsoft DirectX, all before graduating from The University of Texas with a bachelor’s degree in Computer Science. He has also contributed to the Linux kernel, the Open Embedded project, and many more open source projects.
Elvis Collado – Elvis is an up and coming Senior Researcher on Exodus Intelligence’s 0day team. Prior to Exodus, he worked at TippingPoint DVLabs where he researched submissions to the world’s largest and most diverse bug bounty program and developed filters for them. After DVLabs, Elvis worked as a consultant for Praetorian performing penetration tests for large manufacturers of embedded devices. While at Exodus, Elvis has developed several 0day exploits for market leading routers and firewalls.
Date & Location
February 18 through 22nd, 2019: Austin Texas
Requirements
- Laptop
- USB Type-A Ports – You’ll need to be able to use the provided breakout boards
- Disassembler (IDA Pro or radare2)
- Please be familiar with the disassembler you choose.
- Experience with reversing binaries (any architecture)
- VirtualBox or VMWare
- An embedded device of your choice. (Warranties will be voided) Please select a reasonably sized device.
Description
This 5-day course is designed to help students gain the knowledge and experience needed to audit and exploit RTOS and Linux based embedded devices. Students will work through multiple case studies with physical devices to find and exploit each 0day vulnerability found by the trainers. Each case study will use a different device and highlight the approach used to find and exploit each bug. On the last day students will be encouraged to bring in their own device and apply all of the techniques that were taught with guidance from the instructors.
Expectations
Students will be gaining experience with:
- Communicating with common serial protocols.
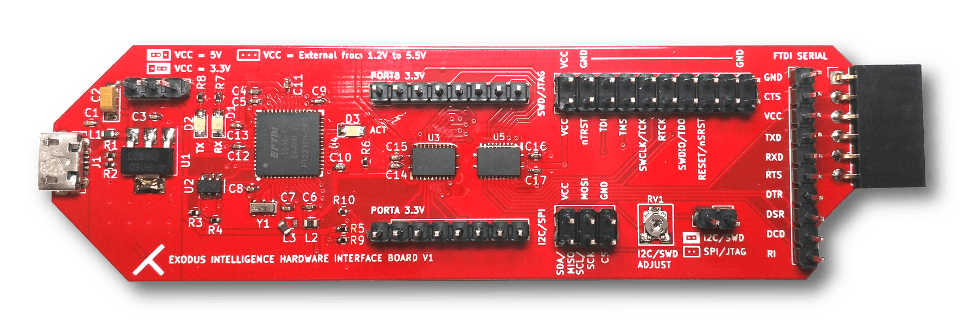
- Utilizing the XI Hardware Interface Board
- MIPS and ARMv7 architectures
- Building custom toolchains
- Organizing JTAG data dumps into something meaningful
- Interpreting Datasheet(s)
- Developing custom shellcode
- Utilizing various methods for extracting firmware
Students will also be given challenges to work on outside of class.
Testimonials
- “David and Elvis are tremendously knowledgeable and do an awesome job on explaining the techniques needed to interface with hardware targets and get to the work we care about: Finding and Exploiting Bugs. This class addresses when exploiting embedded targets is different than traditional targets and how those differences can be leveraged to make exploitation easier. I would definitely recommend this course to anyone getting into embedded exploit development.” – Anonymous Student
- “The Introduction to Embedded Exploitation class provided by Exodus is one of the best technical course I have taken. The instructors are very knowledgeable in hardware and software exploitation and provide a very hands on course that will challenge and advance a security researchers skillset. I would recommend this class to anyone interested in hardware vulnerability research.” – Anonymous Student
- “Exodus Intelligence provides some of the most advanced hands-on training in the field of modern exploit development and reversing “weird machines”.” – @SylerClayton
In The News
- ‘Insight’ into Home Automation Reveals Vulnerability in Simple IoT Product
An in-depth analysis of a vulnerability that was found during the March 2018 training.
Tickets
- To purchase a seat use the link below, or email us at training@exodusintel.com
Note: Tickets will be available for $4500 until January 15th, after that tickets will be priced at $6500.
